 Bruce Schneier says “Remember this: The math is good, but math has no agency. Code has agency, and the code has been subverted.” (read original)
Bruce Schneier says “Remember this: The math is good, but math has no agency. Code has agency, and the code has been subverted.” (read original)
What this means is that the theory behind something — in this case encryption using “hard” mathematics — may be very good, but the implementation can be full of “gotchas” — errors, omissions, faults — and that‘s what will get you in the long term. He was specifically commenting on Edward Snowden’s revelations about the US National Security Agency and whether they can read all encrypted messages, but it can apply to many other software endeavors.
If you’re thinking of writing some software whose function is critical, and especially if lives depend on it, you have to be extremely careful with your implementation. And Open Source is a big plus because other eyes can look at your code and spot mistakes that you, as author, are likely to overlook.
So whatever you’re working on, be very, very careful with the implementation.
 The government of the USA was constituted “to provide for the common defense” among other things.[1] Unfortunately the line between public responsibility and private responsibility for defense in cyberspace could be rather blurry.
The government of the USA was constituted “to provide for the common defense” among other things.[1] Unfortunately the line between public responsibility and private responsibility for defense in cyberspace could be rather blurry.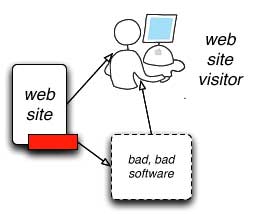 They don’t say this directly—these are my words: Crime, espionage (and warfare) seep into the interstitial spaces of society and occupy any vacuum they find. And from there they can grow to occupy the whole of the space, like a mold, fungus, or rot.
They don’t say this directly—these are my words: Crime, espionage (and warfare) seep into the interstitial spaces of society and occupy any vacuum they find. And from there they can grow to occupy the whole of the space, like a mold, fungus, or rot. In early June, I was in a nice rainy East Coast US city for meetings dealing with particularly thorny issues related to ways the Internet experience is being killed off for regular folks—and for institutions (NGOs) that are promoting free speech and human rights. Over a small breakfast, I sketched in my book some notes about the progression of malware over time. Basically paralleling
In early June, I was in a nice rainy East Coast US city for meetings dealing with particularly thorny issues related to ways the Internet experience is being killed off for regular folks—and for institutions (NGOs) that are promoting free speech and human rights. Over a small breakfast, I sketched in my book some notes about the progression of malware over time. Basically paralleling